In this era of rapid technological advancement, Bitcoin has emerged as a decentralized digital currency with a promising future. However, alongside its rise, the development of quantum computing looms on the horizon, casting a shadow of uncertainty over Bitcoin’s security. This article delves deep into the intricacies of Bitcoin’s current security measures, the fundamental principles of quantum computing, the vulnerabilities that quantum computing poses to Bitcoin, and potential solutions to safeguard its future resilience. By exploring this critical intersection of technology and finance, we aim to provide readers with a comprehensive understanding of the challenges and opportunities that lie ahead for the world’s leading cryptocurrency. So, if you are looking for a website that connects you to investment education firms that can help you along your investment journey, consider visiting a web-based platform.
Understanding Bitcoin’s Security
Cryptography in Bitcoin
Public and Private Keys
Bitcoin users employ public and private keys to send and receive cryptocurrency. Public keys serve as addresses for receiving funds, while private keys act as secret codes to authorize transactions.
Hash Functions
Bitcoin employs cryptographic hash functions to ensure data integrity and secure transactions. These one-way functions convert data into a fixed-length string, making it virtually impossible to reverse-engineer the original data.
Digital Signatures
Digital signatures provide authenticity and verify the sender’s consent in Bitcoin transactions. They ensure that the transaction has not been tampered with during transmission.
How Bitcoin Transactions Work
Bitcoin transactions are recorded on the blockchain, a public ledger. Miners validate transactions and secure the network by solving complex mathematical puzzles.
Why Bitcoin is Considered Secure Today
Bitcoin’s security lies in the robustness of its cryptographic techniques, making it challenging for conventional computers to breach. However, the advent of quantum computing raises concerns.
Quantum Computing Basics
What is Quantum Computing?
Quantum computers leverage quantum bits or qubits, which can exist in multiple states simultaneously, enabling exponential processing power.
Quantum Computing vs. Classical Computing
Quantum computers outperform classical computers in specific calculations, particularly those involving factoring large numbers into prime factors.
Shor’s Algorithm: A Threat to Cryptography
Shor’s Algorithm, devised by mathematician Peter Shor, poses a significant threat to classical cryptographic methods. It can efficiently factor large numbers, breaking the encryption used in Bitcoin and other cryptocurrencies.
The Vulnerabilities of Bitcoin to Quantum Attacks
Shor’s Algorithm and Bitcoin’s Encryption
The most vulnerable aspect of Bitcoin is its dependence on cryptographic techniques that Shor’s Algorithm can crack. Quantum computers can potentially decipher private keys, rendering Bitcoin wallets vulnerable to theft.
Attacking Bitcoin’s Hash Functions
Quantum computers can also compromise Bitcoin’s hash functions, potentially altering transaction data and undermining the integrity of the blockchain.
The Implications for Bitcoin’s Security
These vulnerabilities could lead to double-spending attacks, theft of funds, and a loss of trust in the Bitcoin network. As quantum computing matures, these risks become more imminent.
Potential Solutions and Mitigations
Post-Quantum Cryptography
Overview of Post-Quantum Cryptographic Algorithms
Researchers are actively developing post-quantum cryptographic algorithms that are resistant to quantum attacks. These include lattice-based, code-based, and multivariate polynomial cryptography.
Implementing Post-Quantum Cryptography in Bitcoin
To secure Bitcoin’s future, the cryptocurrency community must transition to post-quantum cryptographic algorithms. This involves a coordinated effort to update wallets, nodes, and mining software.
Quantum-Resistant Blockchains
Some projects are exploring the creation of quantum-resistant blockchains, designed from the ground up to withstand quantum threats. These innovative networks aim to provide a more secure alternative to Bitcoin.
The Role of Quantum-Safe Wallets
Developers are designing quantum-safe wallets that can protect users from quantum attacks. These wallets will use quantum-resistant cryptographic techniques to safeguard private keys.
Challenges and Concerns
Adoption of Quantum-Resistant Solutions
The adoption of quantum-resistant solutions in the Bitcoin ecosystem may be slow and challenging, as it requires consensus among the community and a substantial upgrade of the network.
Transitioning from Traditional Cryptography
Switching from traditional cryptographic methods to post-quantum alternatives is a complex process that must be executed carefully to prevent security breaches.
Uncertainties Surrounding the Quantum Threat
The timeline for the development and widespread deployment of quantum computers remains uncertain, complicating efforts to prepare for the quantum threat effectively.
Future of Bitcoin in a Quantum World
Quantum Computing’s Timeline and Bitcoin’s Security
The timeline for the arrival of practical quantum computers is uncertain, making it challenging to determine how quickly Bitcoin must adapt to remain secure.
Collaboration and Research Efforts
The cryptocurrency community and researchers must collaborate to stay ahead of quantum threats, investing in ongoing research and development of quantum-resistant technologies.
The Importance of Staying Informed
Staying informed about developments in quantum computing and Bitcoin’s security measures is crucial for users, developers, and stakeholders to make informed decisions.
Conclusion
In conclusion, the looming threat of quantum computing poses a substantial challenge to Bitcoin’s security, necessitating a proactive shift towards quantum-resistant technologies and cryptographic methods. As the digital landscape continues to evolve, Bitcoin’s resilience depends on its ability to adapt and stay ahead of emerging threats, ensuring the continued trust and viability of the world’s leading cryptocurrency.
DISCLAIMER: This article is a partnered post and does not substitute for professional advice or help. Any action you take based on the information presented in this article is strictly at your own risk and responsibility.
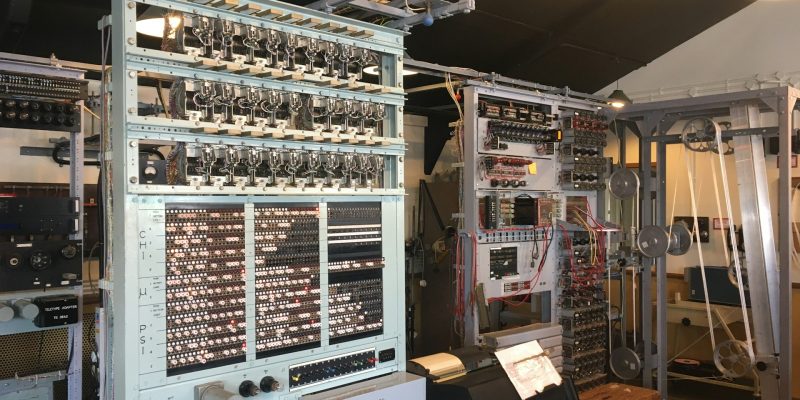
Feature Photo by Farai Gandiya on Unsplash





Comments